Critical infrastructure has always faced a dilemma: how to capture valuable data without compromising national security? DJI is here to resolve this paradox, redefining data security in critical environments through a security protocol based on the philosophy: “Data Under Control. Infrastructure Protected.”
The Era of Data Security
DJI not only recognizes the importance of data sovereignty but also places it at the center of its operational strategy. By implementing government-grade security protocols and undergoing rigorous independent audits, organizations can:
- Operate with full transparency regarding where and how data is stored;
- Ensure compliance with national security and critical infrastructure regulations;
- Maintain absolute control over sensitive data captured during critical operations.
All while maintaining the operational efficiency that drone technologies provide.
Data Control Without Compromise
The greatest advantage of the DJI 2026 security protocol is its “user-controlled data” approach.
- Explicit Permissions: DJI does not access any user data without explicit consent. This fundamental principle ensures that critical infrastructure organizations maintain full control over sensitive information.
- End-to-End Encryption: All data transmitted between the drone and the ground control station is protected with AES-256 encryption, preventing interception or unauthorized access during real-time operations.
- Geographically Controlled Storage: Data from operators outside China is stored exclusively on servers located in the U.S. For agricultural and specialized operations, DJI offers storage options on servers in the U.S., Japan, or Europe, enabling compliance with data residency regulations.
- Proprietary OcuSync Protocol: A communication system developed in-house by DJI with built-in encryption, creating a secure, dedicated communication channel that does not rely on third-party communication infrastructure.
- Configurable Security Mode: During initial setup, operators choose the security mode that best suits their needs—ranging from standard commercial operations to enhanced modes for critical infrastructure.
Compliance Verified by Independent Third Parties
The credibility of DJI’s security does not rest on internal claims. Since 2017, independent audits by international cybersecurity firms and government agencies have rigorously validated our security protocols.
Three Key Certifications:
NIST FIPS 140-2 (2022): The DJI Core Crypto Engine—the central cryptographic engine that protects all sensitive data—has been certified by the National Institute of Standards and Technology. This is the most rigorous standard for cryptographic modules, used by U.S. federal agencies.
ISO 27001 (2023): DJI FlightHub 2 has received ISO 27001 certification, validating that its design, development, and operational services comply with international information security management standards.
FTI Cybersecurity Audit (2024): A comprehensive independent audit of the Mavic 3T, Pilot 2, and RC Pro systems, confirming that U.S. operators can trust the security protocols when selecting enhanced safety modes.
Additionally, agencies such as the U.S. Department of the Interior and the Idaho National Laboratory, as well as firms such as Booz Allen Hamilton and TÜV SÜD, have conducted independent validations that confirmed the integrity of DJI’s security protocols.
Multisectoral Engineering for Critical Infrastructure
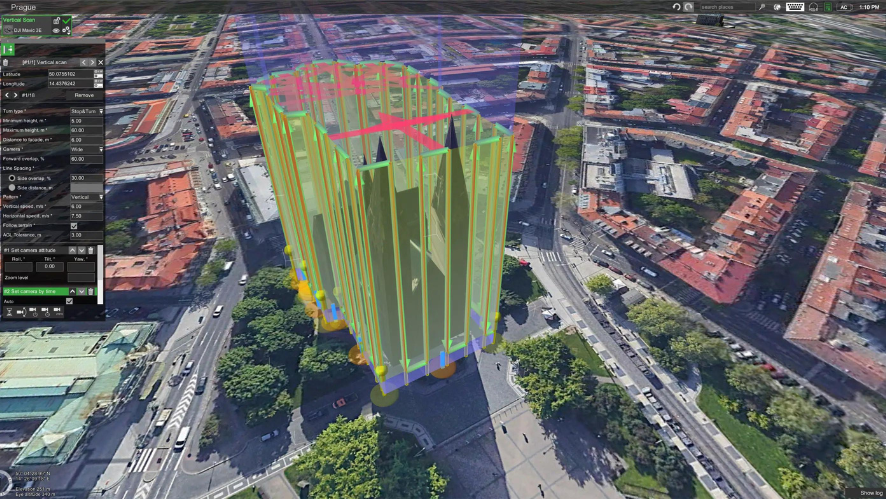
The DJI 2026 security protocol is designed to protect operations across multiple critical sectors:
- Energy Infrastructure Inspection: Power lines, substations, and solar facilities can be inspected while critical data remains under local control, without transmission to unauthorized remote servers.
- Perimeter Surveillance and Physical Security: Surveillance operations at sensitive facilities generate data that remains encrypted and under the operator’s control, with options for full offline storage.
- Port and Airport Infrastructure Maintenance: Structural inspection data can be captured, encrypted, and stored locally, complying with critical security regulations.
- Emergency Response Operations: In crisis situations, drone data can be captured and used without concerns about transmitting sensitive data to third parties.
- Investigation and Forensics: Forensic data captured by drones maintains a digital chain of custody through encryption and cryptographic signatures.
Layered Security Architecture
The DJI 2026 protocol implements multi-layered security:
- Device Layer: Secure Boot protects software integrity, Secure Key Management ensures that cryptographic keys are never exposed, and Secure Storage protects sensitive data on the device.
- Communication Layer: OcuSync with AES-256 protects all data transmitted between the drone and the controller, preventing interception or unauthorized access.
- Storage Layer: Data can be stored locally on the drone, on the controller, or in a private cloud. Users choose the architecture that best suits their security needs.
- Access Control Layer: Granular permissions ensure that only authorized users can access specific data. Audit logs track all access.
- Compliance Layer: Compliance with GDPR, national data regulations, and critical infrastructure requirements is built-in, not an add-on.
Secure Wiping and Total Control
Operators maintain total control over data through secure wiping capabilities. Data can be wiped from the device, controller, or cloud with a single command: “Clear All Device Data” via DJI Pilot 2. This feature ensures that sensitive data never remains on the system longer than necessary.
The Future of Data Sovereignty
In a market that demands absolute security, regulatory compliance, and verifiable data control, the DJI 2026 security protocol positions critical infrastructure operations at the forefront of protection. It’s not just about encryption; it’s about a security architecture that puts the user in control.
DJI believes that the future of critical infrastructure is one where advanced technology and data sovereignty are not trade-offs, but complementary. With the 2026 security protocol, sensitive data can be captured, protected, and controlled without sacrificing operational efficiency.
Are you ready to implement verifiable data security in your critical operations?